M&A Cyber Due Diligence
Cyber risk, priced into the deal.
Pre-acquisition diligence and post-close integration for PE sponsors, corporate acquirers, and investment banks — translated into deal language, not technical jargon.
-
15 years as CSO at Silicon Valley Bank, the bank of the innovation economy
-
$200B+ in assets defended at enterprise scale
-
Design partner to Palo Alto Networks, Zscaler, CrowdStrike, FireEye, and Eclypsium
-
Author of Cyber War and Peace; board member, Bay Area CSO Council
-
Trusted advisor to PE/VC firms, cyber product companies, and enterprise boards
-
15 years as CSO at Silicon Valley Bank, the bank of the innovation economy
-
$200B+ in assets defended at enterprise scale
-
Design partner to Palo Alto Networks, Zscaler, CrowdStrike, FireEye, and Eclypsium
-
Author of Cyber War and Peace; board member, Bay Area CSO Council
-
Trusted advisor to PE/VC firms, cyber product companies, and enterprise boards
-
15 years as CSO at Silicon Valley Bank, the bank of the innovation economy
-
$200B+ in assets defended at enterprise scale
-
Design partner to Palo Alto Networks, Zscaler, CrowdStrike, FireEye, and Eclypsium
-
Author of Cyber War and Peace; board member, Bay Area CSO Council
-
Trusted advisor to PE/VC firms, cyber product companies, and enterprise boards
What’s Included
A cyber diligence deliverable that belongs in the data room. Risk quantified in dollars. SPA and insurance terms informed by a senior operator. Post-close remediation with accountability.
Quantify cyber risk in deal terms
Estimated loss ranges, remediation cost, regulatory exposure — translated into language the IC and deal committee actually use.
Assess the target’s real posture
External attack surface, control maturity, incident history, third-party dependencies, and key-person risk. Surface what the seller didn’t disclose.
Inform SPA and insurance terms
Security reps and warranties, indemnity scope, escrow, and RWI coverage — drafted with cyber risk priced in.
Run the 100-day plan post-close
Remediation roadmap, interim CISO support, and portfolio onboarding so the cyber risk surfaced in diligence actually gets fixed.
Typical engagement: 5-day Initial Review for bid/IC decisions, deeper post-LOI diligence on 2–4 week cadence, optional 100-day post-close roadmap.
The Proprietary Differentiator
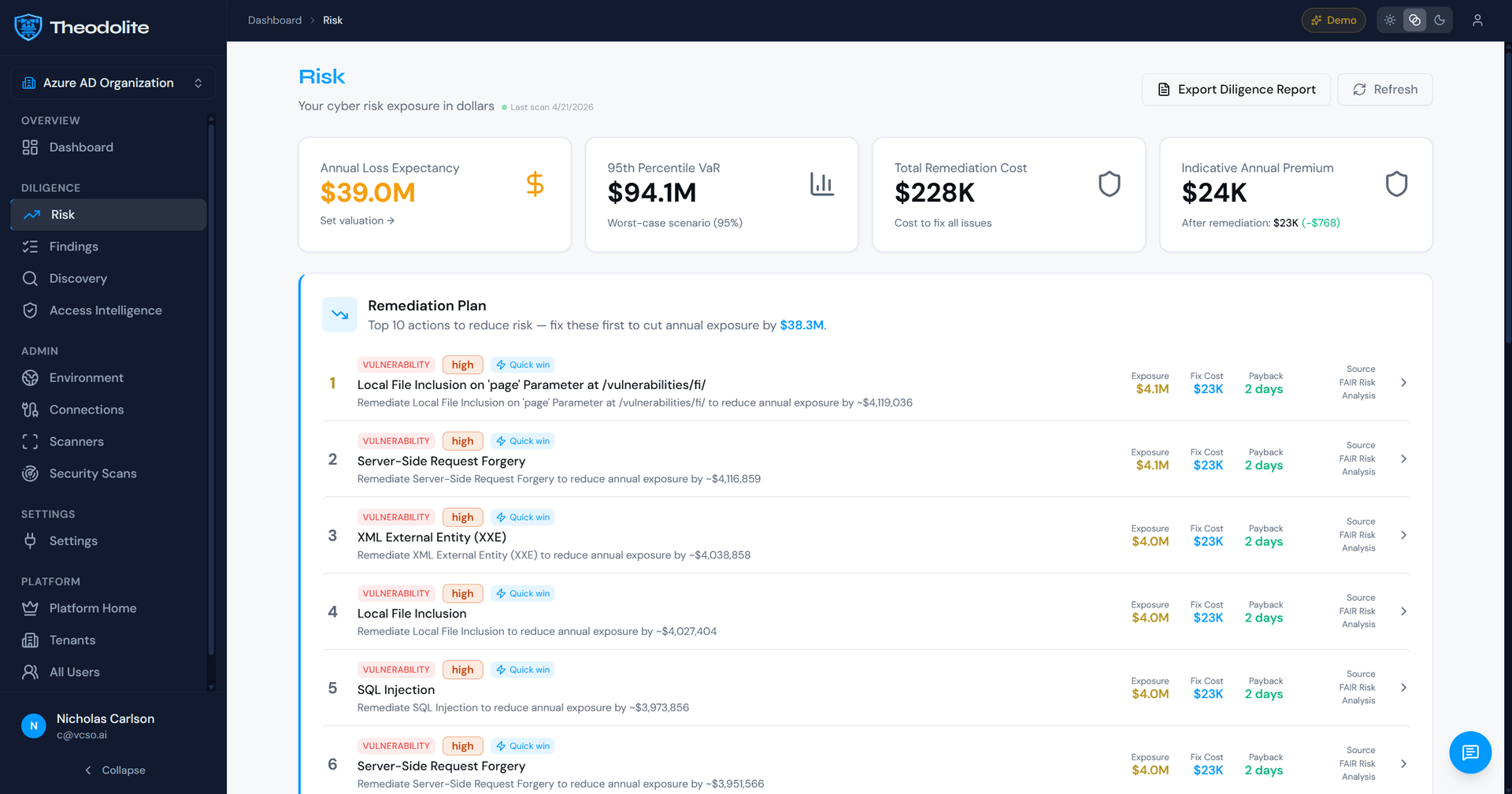
Powered by Theodolite™
Theodolite is our proprietary AI security intelligence platform. It runs the external attack-surface review, control-maturity scoring, and exposure quantification that typically take consultant teams weeks — in the language the IC actually uses: estimated loss, remediation cost, and deal impact.
Every diligence engagement is Theodolite-accelerated. The 5-day Initial Review, the post-LOI deep assessment, and ongoing portfolio readiness checks all lean on the platform to surface risk at deal speed — and on our senior operators to translate it into SPA terms.
Learn more about Theodolite →How It Works
-
Initial Risk Review — 5-Day Turnaround
Theodolite-accelerated exposure scan across the target’s public attack surface, disclosed incidents, compliance posture, and key technology stack. Delivered as a go/no-go memo suitable for the IC or deal committee.
-
Deep Diligence Assessment
Full posture review: control maturity, regulatory status, incident history, key-person risk, third-party dependencies. Findings are quantified (likely loss, remediation cost, deal impact) and integrated into the valuation and SPA negotiation.
-
Post-Close Integration & Portfolio Support
Remediation roadmap, 100-day plan, and ongoing advisory into the portfolio. For serial acquirers and platform builders, we carry institutional memory across deals so the next diligence is faster and sharper.
Who This Is For
Built for the deal side of the table — sponsors, acquirers, and advisors who need credible cyber diligence that maps to valuation, terms, and post-close execution.
-
Private Equity Sponsors
Evaluating a cybersecurity posture as part of deal diligence, or carrying an inherited risk problem in the portfolio.
-
Corporate Acquirers
Strategics doing bolt-on acquisitions where cyber exposure is a material risk to the deal thesis or the buyer’s regulatory footprint.
-
Investment Banks
Sell-side advisors who need a credible cyber diligence partner to pre-empt buyer findings and protect valuation.
-
Family Offices & LPs
Direct investors looking for an independent risk opinion before committing to a control or minority position.
Leadership You Can Trust
Most advisors diagnose. Operators prescribe.
vCSO.ai is led by Nick Shevelyov — 15-year Chief Security Officer at Silicon Valley Bank, the bank of the innovation economy. Design partner to Palo Alto Networks, Zscaler, CrowdStrike, FireEye, and Eclypsium. Author of Cyber War and Peace. Board member, Bay Area CSO Council.

Achievements
- Defended Silicon Valley Bank’s cyber posture for 15 years (2007-2021), through every major crisis from the 2008 financial collapse to SolarWinds.
- Design partner and advisor to category-defining cybersecurity companies including Palo Alto Networks, Zscaler, CrowdStrike, FireEye, and Eclypsium.
- Forbes Technology Council member, NASDAQ board director (AuthID), author of Cyber War…and Peace.
- Founder of the CISO Supper Club, convening Bay Area cybersecurity executives twice a year.
Who You’ll Work With
Led by Nick, supported by specialists in assessment, compliance, and operations — one relationship, full bench.

Andrej
CISSP, ethical hacker (assessments and pen testing)

Berk
GRC specialist (compliance frameworks)

Nicholas
Operations and Website

Sonija
Operations and Accounting
FAQ
Questions deal teams ask before engaging.
How fast can you deliver an initial review?
The 5-day Initial Review is standard. Rush turnarounds (48–72 hours) are possible for time-sensitive bids; we’ll confirm scope and feasibility on intake.
What goes into the deliverable?
A memo and appendices covering: external attack-surface findings, control-maturity scoring, regulatory and compliance status, incident disclosure history, estimated loss and remediation cost ranges, and red-flag items that warrant seller response before close.
Do you work with the target or around them?
Both modes. External-only reviews are standard pre-LOI and confidential bids. Management-access diligence (post-LOI) is deeper and yields materially better quantification.
How is this different from what our IT consultant does?
IT consultants run technical audits. Cyber diligence translates technical findings into deal language: impact on valuation, SPA representations, reps-and-warranties insurance posture, and post-close remediation budget. The audience is the deal committee, not the CTO.
Can you stay on after close?
Yes — and many of our best outcomes do. Post-close we run the 100-day remediation, support the portfolio CISO hire, and serve as the institutional memory across subsequent acquisitions.
Ready to price cyber risk into your next deal?
The 5-day Initial Review delivers a go/no-go memo fit for the IC. Deeper diligence follows post-LOI. Every engagement is Theodolite-accelerated, so you get senior-practitioner findings at deal speed.

